The global payments ecosystem is expanding at unprecedented speed. With the rise of cross-border commerce, embedded finance, and alternative payment methods (APMs), moving money has never been easier. However, this frictionless digital economy has introduced a massive counter-weight: the overwhelming complexity of payments compliance.
In the past, achieving payments compliance simply meant keeping credit card numbers secure. Today, it is a multi-disciplinary operational mandate that intersects cybersecurity, identity verification, anti-money laundering (AML), and localized data privacy laws.
For FinTechs, marketplaces, and global enterprises, treating compliance as an afterthought is a fatal error. Regulatory fines for non-compliance regularly reach hundreds of millions of dollars, not to mention the catastrophic loss of consumer trust.
Whether you are a developer integrating a new payment gateway or a Chief Risk Officer mapping out international expansion, this guide unpacks the four critical pillars of modern payments compliance and how to build a risk-proof infrastructure.
What is Payments Compliance?
At its core, payments compliance is the set of regulations, industry standards, and legal frameworks that organizations must adhere to when processing, storing, or transmitting financial transactions.
The primary goals of payments compliance are to:
-
Protect Consumer Data: Prevent unauthorized access to sensitive financial information (like PANs and CVVs).
-
Prevent Financial Crime: Stop bad actors from using the financial system for money laundering, terrorist financing, or fraud.
-
Ensure Fair Competition and Transparency: Maintain a level playing field through open banking and standardized consumer protections.
To achieve these goals, organizations must navigate a web of overlapping requirements. We can break these down into four distinct pillars.
Pillar 1: Information Security & Payment Card Industry Standards (PCI DSS)
If your business touches a credit or debit card, you fall under the jurisdiction of the Payment Card Industry Data Security Standard (PCI DSS). Formed by Visa, Mastercard, Discover, and Amex, this global standard dictates exactly how payment data must be handled.

The Shift to PCI DSS v4.0
The compliance landscape recently underwent a massive shift with the rollout of PCI DSS v4.0. Unlike previous iterations that relied on rigid, checklist-based controls, v4.0 introduces a customized approach, focusing heavily on continuous security rather than annual audits. It places strict new requirements on multi-factor authentication (MFA), targeted risk analysis, and the monitoring of e-commerce skimming attacks (Magecart).
Tokenization and Payment Orchestration
For most businesses, achieving high-level PCI compliance (like Level 1) internally is technically exhausting and prohibitively expensive. This is why modern architecture relies heavily on tokenization and payment orchestration.
Instead of storing raw credit card numbers on your own servers, tokenization swaps the sensitive data for a mathematically irreversible token. Payment orchestration layers take this a step further. By utilizing an independent, PCI-compliant vault, businesses can securely store payment methods and route transactions across dozens of different payment gateways (like Stripe, Adyen, or PayPal) without the sensitive data ever touching their own internal servers. This effectively reduces your PCI scope to near zero while maintaining complete control over your payment stack.
Related Content MarketPlace
Pillar 2: Identity Verification (KYC & KYB)
Before you can legally process a payment for a user or disburse funds to a merchant, you must know exactly who you are dealing with. Identity verification is the frontline defense of payments compliance.

Know Your Customer (KYC)
KYC is a mandatory process for financial institutions and payment service providers to verify the identity of their end-users. A robust KYC flow goes beyond basic data entry; it requires:
-
Document Verification: Using optical character recognition (OCR) to validate government-issued IDs, passports, or driver’s licenses.
-
Biometric Liveness Detection: Ensuring the person presenting the ID is a live human being, not a deepfake, photo, or mask.
-
Watchlist Screening: Checking the individual against global sanctions lists (e.g., OFAC) and Politically Exposed Persons (PEP) databases.
Know Your Business (KYB)
For B2B platforms, SaaS companies, and marketplaces, KYB is equally critical. You cannot simply verify the business name; compliance dictates that you must drill down to identify the Ultimate Beneficial Owners (UBOs)—the actual humans who hold a controlling stake (usually 25% or more) in the company.
The challenge with KYC and KYB is friction. If your verification process takes days, users will abandon your platform. Modern compliance platforms leverage automated APIs to ping global identity databases in milliseconds, balancing strict security with a seamless onboarding experience.
Pillar 3: Anti-Money Laundering (AML) and Transaction Monitoring
While KYC occurs at the point of onboarding, AML is a continuous, ongoing process. Bad actors frequently use legitimate-looking accounts to layer and integrate illicit funds. Payments compliance requires you to actively monitor the flow of money to catch these activities in real-time.
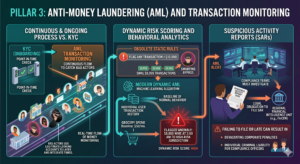
Dynamic Risk Scoring and Behavioral Analytics
Static, rules-based AML systems are obsolete. In the past, an AML rule might be: “Flag any transaction over $10,000.” Money launderers easily bypass this by simply structuring their payments into smaller chunks (e.g., $9,999), a process known as smurfing.
Today, payments compliance relies on dynamic transaction monitoring. This involves leveraging machine learning algorithms to establish a baseline of “normal” behavior for every individual user. If a user who typically spends $50 a month on groceries suddenly attempts to wire $8,000 to a high-risk jurisdiction at 3:00 AM, the system automatically flags the anomaly.
Suspicious Activity Reports (SARs)
When a transaction triggers an AML alert, compliance teams must investigate. If the activity is deemed illicit, the organization is legally obligated to file a Suspicious Activity Report (SAR) with their regional financial intelligence unit (such as FinCEN in the United States). Failing to file a SAR—or filing it late—can result in devastating corporate penalties and individual criminal liability for compliance officers.
Our Portfolio Makeuser
Pillar 4: Regional Regulations, Open Banking, and Data Privacy
Payments compliance is not a monolithic global standard; it changes drastically depending on the geographic location of your users.

PSD2 and Strong Customer Authentication (SCA)
In the European Union, the Revised Payment Services Directive (PSD2) fundamentally altered the payments landscape. Its most impactful component is the requirement for Strong Customer Authentication (SCA). To process an electronic payment in the EU, the transaction must be authenticated using at least two of the following three elements:
-
Something the user knows: (A password or PIN).
-
Something the user has: (A smartphone or hardware token).
-
Something the user is: (A fingerprint or facial recognition).
Failing to implement SCA protocols (like 3D Secure 2.0) will result in soft declines directly from European issuing banks.
Data Privacy: GDPR, CCPA, and Beyond
Payment data is inherently personal data. Therefore, payments compliance must operate in lockstep with data privacy laws like the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the US.
This creates a complex regulatory paradox. AML laws require you to retain user data for years to assist in historical financial crime investigations. However, GDPR grants users the “right to be forgotten,” allowing them to request the deletion of their personal data. Navigating this intersection requires sophisticated data governance architectures that know exactly when retention mandates override privacy requests.
The Role of AI and RegTech in the Future of Compliance
Attempting to manage PCI, KYC, AML, and local regulations manually using spreadsheets and human analysts is a guaranteed path to failure. The volume and velocity of digital payments have simply outpaced human capacity.
This is where RegTech (Regulatory Technology) and Artificial Intelligence step in.
Leading organizations are transforming their compliance programs into automated revenue enablers rather than bureaucratic bottlenecks. By implementing AI-driven compliance workflows, businesses can:
-
Automate up to 90% of manual KYC document reviews.
-
Drastically reduce “false positives” in AML transaction monitoring, freeing up human analysts to investigate actual threats.
-
Automatically route transactions to alternative payment processors if one gateway is experiencing a compliance-related outage.
Conclusion: Building a Culture of Compliance
Payments compliance is no longer just a legal checklist; it is a fundamental pillar of your product architecture and brand reputation. When users hand over their credit card details or their passports, they are extending an incredible amount of trust.
To thrive in the modern financial ecosystem, businesses must stop viewing compliance as a hurdle. By leveraging payment orchestration for PCI scope reduction, automating KYC/KYB onboarding, and deploying AI-driven transaction monitoring, organizations can build a payments infrastructure that is secure, globally scalable, and inherently risk-proof.

